4.0
Azure
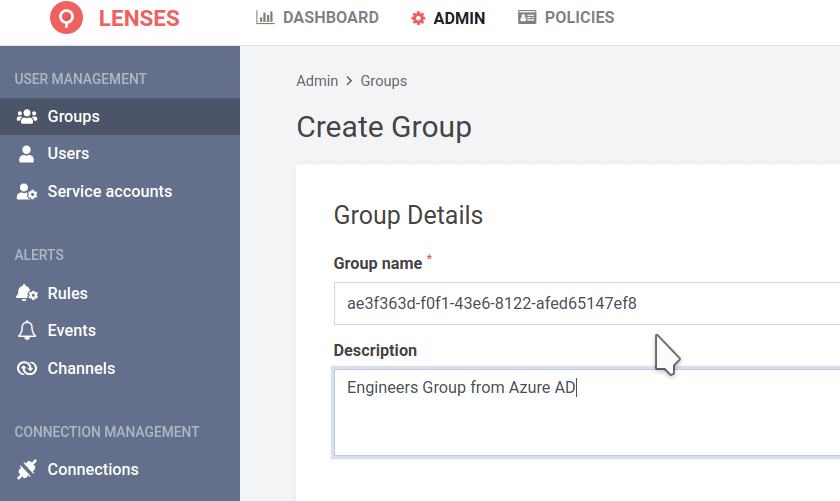
Map groups to Lenses
Groups are case-sensitive and mapped by UUID with Azure
Integrate your user-groups with Lenses using the Azure group IDs. The group IDs are in universally unique identifier ( UUID) format. Create a group in Lenses using the UUID as the name.
For example, if the Engineers group has the UUID ae3f363d-f0f1-43e6-8122-afed65147ef8, create a group with the
same name:
To learn how to use data centric permissions for users and service accounts check the help center .
Setup Microsoft Azure SSO
Learn more about Azure SSO
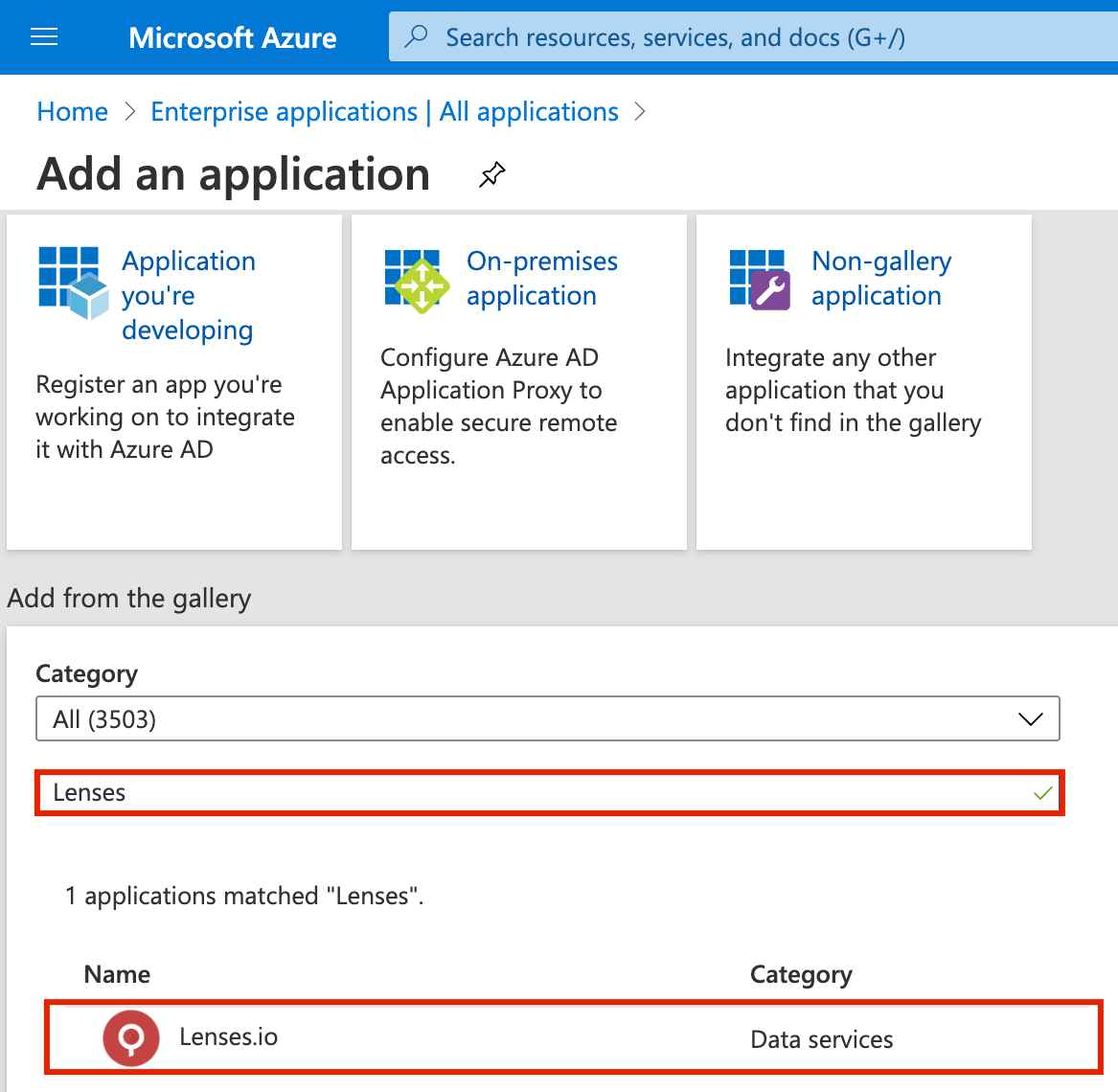
Add from Azure app-gallery
- Go to Enterprise applications > + New Application
- Search for Lenses.io in the gallery directory
- Choose a name for Lenses e.g. Lenses.io and click Add
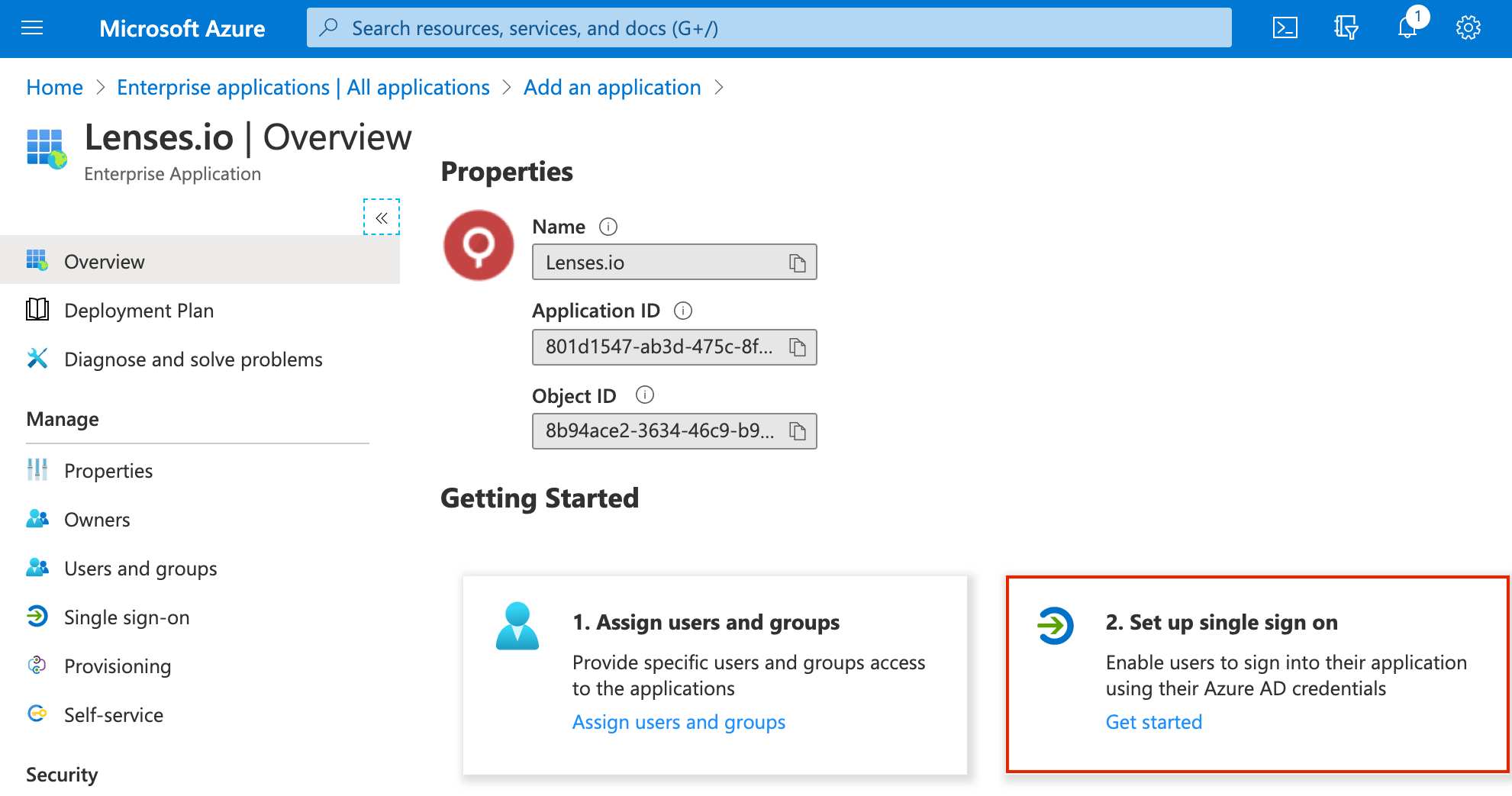
Enable Single-Sign-On
Select Set up single sign on > SAML
Configure your SAML details:
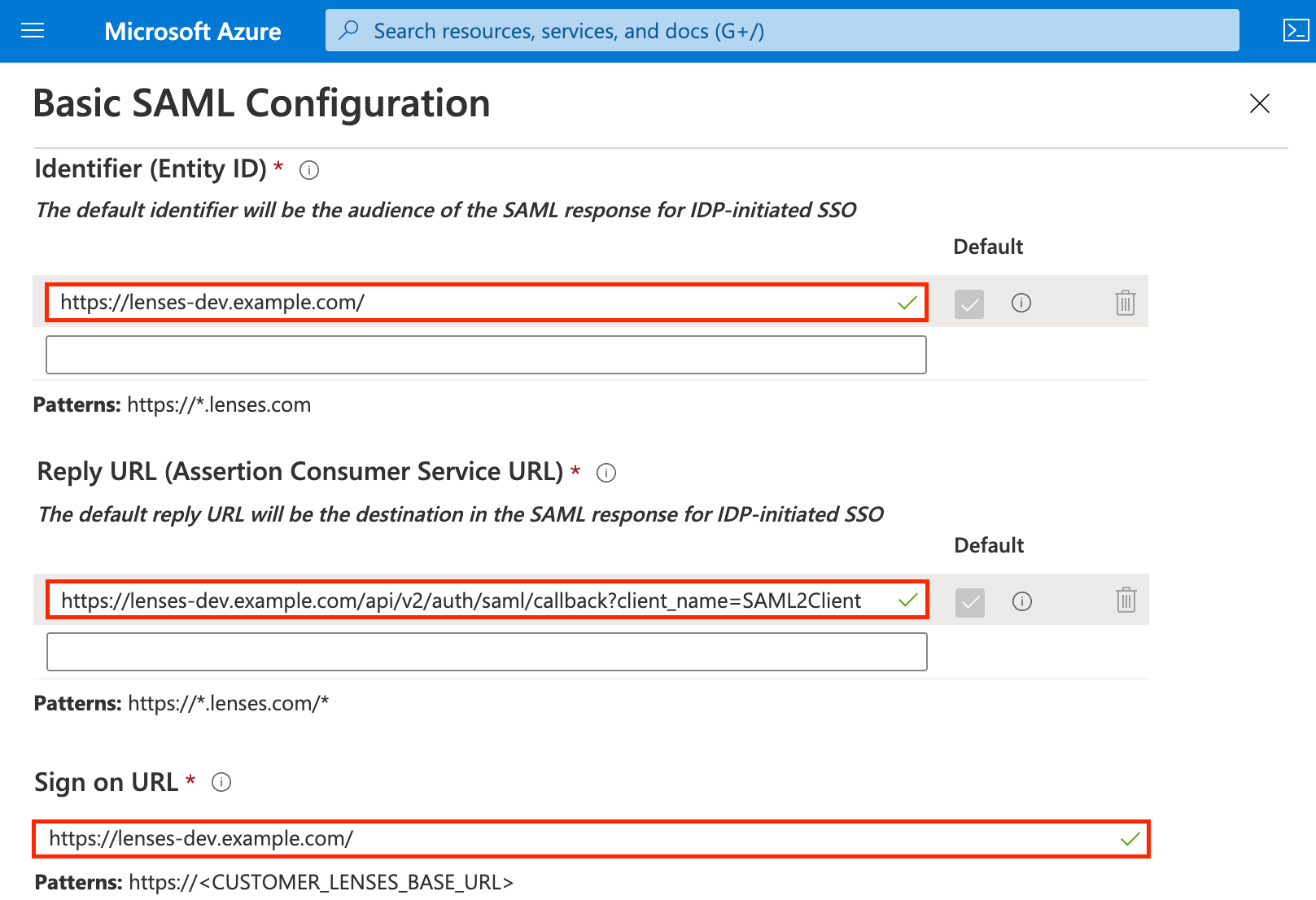
| Setting | Value |
|---|---|
| Identifier (Entity ID) | Use the base url of the Lenses installation e.g. https://lenses-dev.example.com |
| Reply URL | Use the base url with the callback details e.g. https://lenses-dev.example.com/api/v2/auth/saml/callback?client_name=SAML2Client |
| Sign on URL | Use the base url |
Remember to activate HTTPS on Lenses. See TLS .
Download SAML Signing Certificate
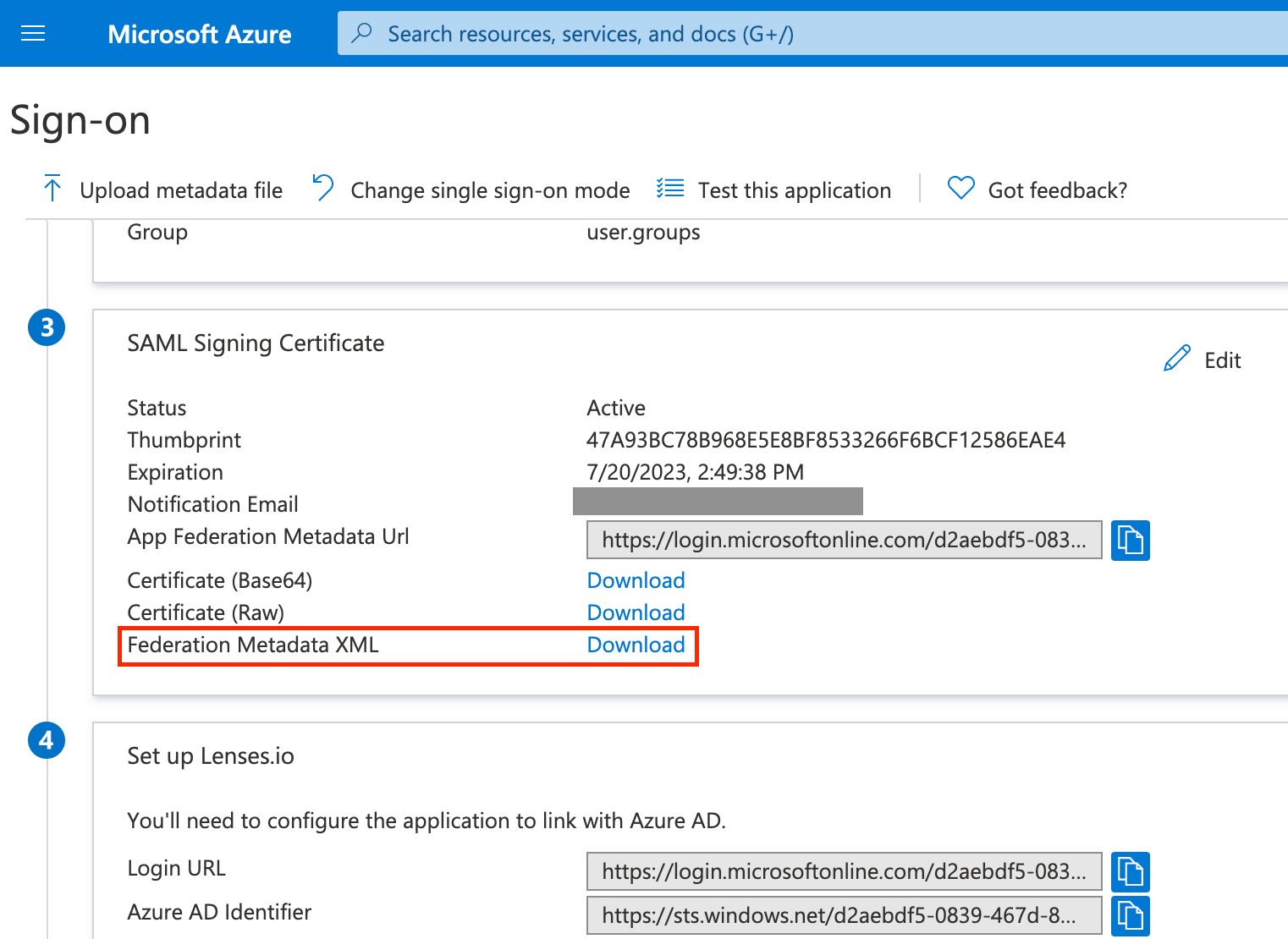
Download the Federation Metadata XML file with the Azure IdP details. You will reference this file’s path in the Lenses
security.conf configuration file.
lenses.security.saml.idp.metadata.file="/path/to/AzureIDPMetadata.xml"
Configure Lenses
Given the
downloaded metadata file and a
keystore
, add the
following configuration to security.conf:
lenses.security.saml.base.url="https://lenses-dev.example.com"
lenses.security.saml.idp.provider="azure"
lenses.security.saml.idp.metadata.file="/path/to/AzureIDPMetadata.xml"
lenses.security.saml.keystore.location = "/path/to/keystore.jks"
lenses.security.saml.keystore.password = "my_keystore_password"
lenses.security.saml.key.password = "my_saml_key_password"
See all SSO options .
